Category: Computers
-
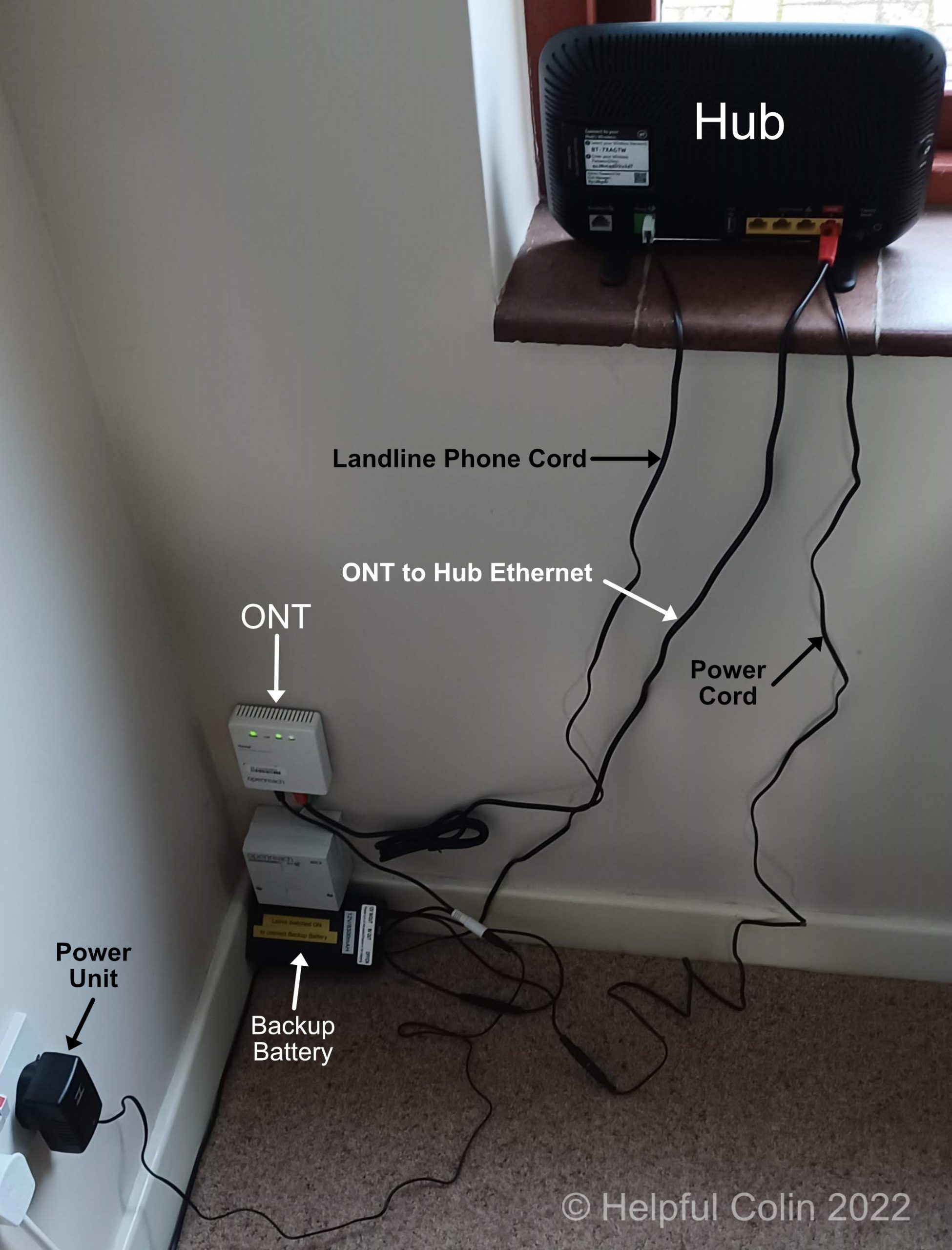
My Broadband Hub & Phone Have A Backup Battery
To guard against power cuts this winter I have given my Broadband Hub and fibre to ethernet interface (ONT) a 3-hour Backup Battery.
-

14 Pin & 15 Pin D Connectors on VGA Cables
Introduction I wanted to know what the difference is between VGA cables with 14 pin and 15 “D” connectors. I found the answer on the Instructables site/forum. The info I needed was contained in a reply to a query by onrust circa 2010.
-

Cooling Fan Lubrication For An NVIDIA GeForce GTS240
Preface This post describes: My success at cooling fan lubrication on an NVIDIA GeForce GTS240 PC display adapter to silence it when it became noisy.
-

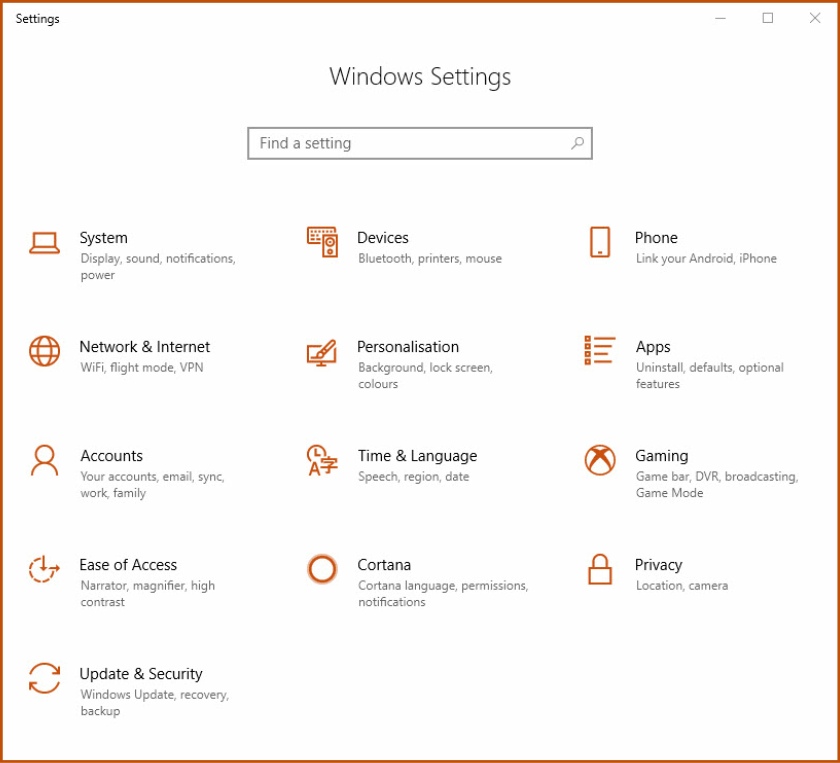
Windows 10 File History Used To Backup My PC
Introduction Since the introduction of Windows 10 version 1709, and acquiring a new backup drive, I have chosen to use Windows 10 File History to backup my PC. So far so good. I have used it to backup my data and to restore some.. I will describe how this tool is used from my point…
-

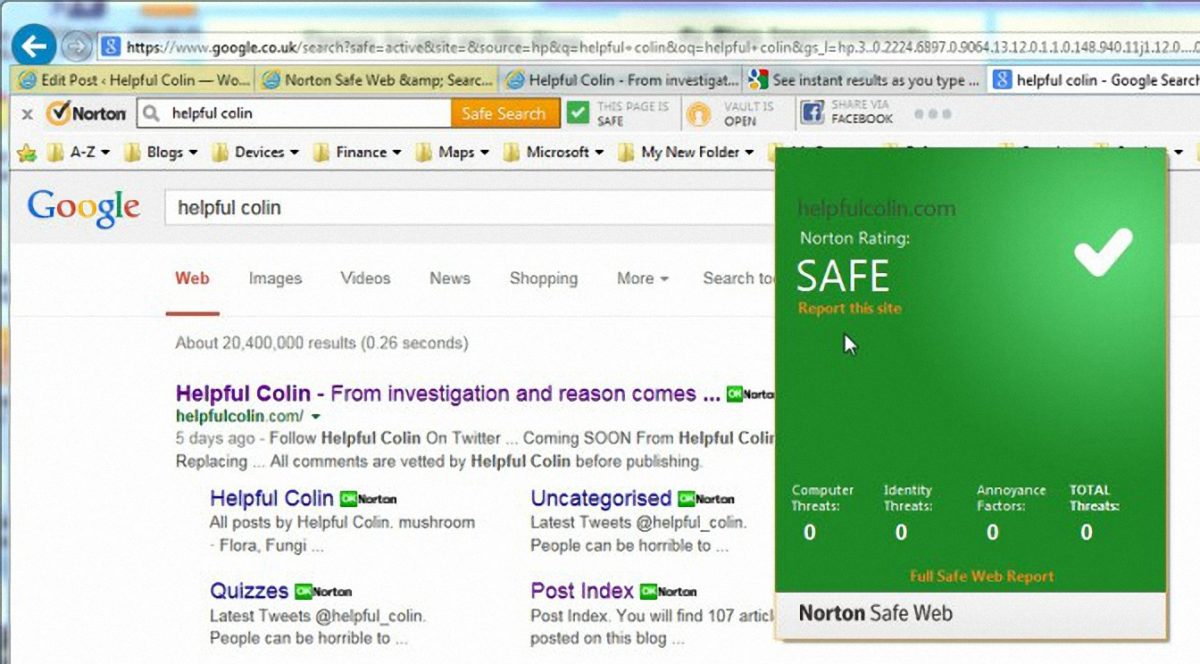
Discussing Malicious Website URLs On Twitter
Introduction I have recently come across an issue where good people wish to convey information about malicious websites to everyone. They’re doing very good work tying to keep us all safe and informed by discussing malicious website URLs (Universal Resource Locators), particularly on Twitter. Unfortunately Twitter creates a link in the text to anything looking…
-
LastPass Password Phishing Exploit
The LastPass password phishing exploit could trick users into giving away their password. If you use LastPass check this exploit out at The Hacker Blog and IT Pro. It involves unscrupulous people phishing for LastPass passwords. Update for LastPass Password Phishing Exploit This issue is now fixed for all the latest versions of Lastpass on Chrome…
-
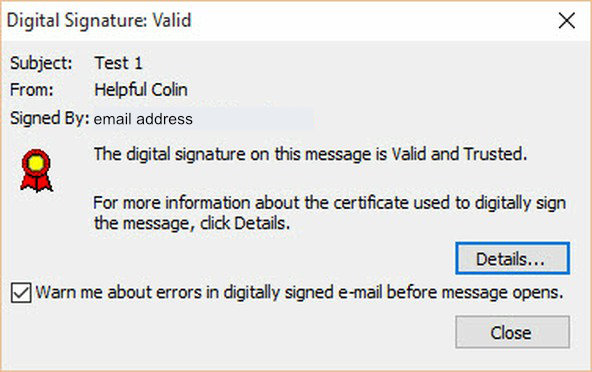
Using A Digital Signature With Outlook
Introduction This article covers some of the issues involved when using a Digital Signature. Each Digital Signature is generated from a Digital Certificate (otherwise known as a Digital ID) issued by a certifying authority. All examples given are created using Microsoft Outlook 2010 on a PC using Microsoft Windows 10, but the principles apply to other versions of…
-
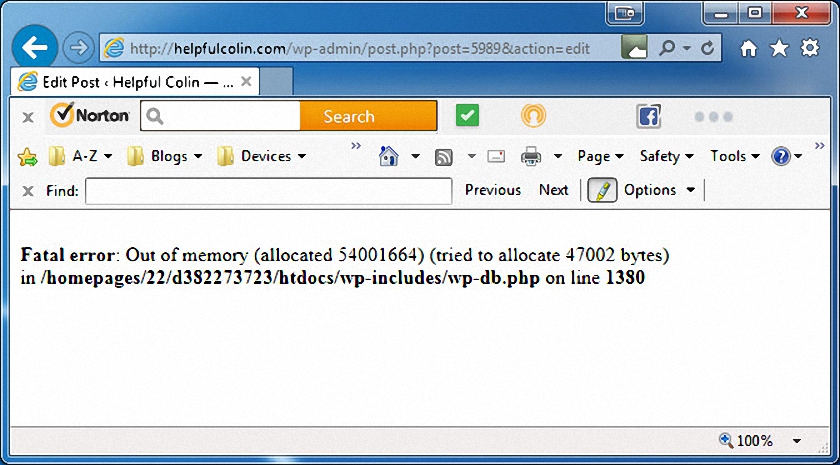
WordPress Fatal Error Out of Memory
How I Resolved ‘Fatal Error Out of Memory’ For A Single Post After much editing of my WordPress post entitled ‘How A Toilet Silent Fill Valve Works’, since I wrote it in May 2014, (there must have been at least 150 edits, and I changed it from a page to a post too) I suddenly had this ‘Fatal…
-
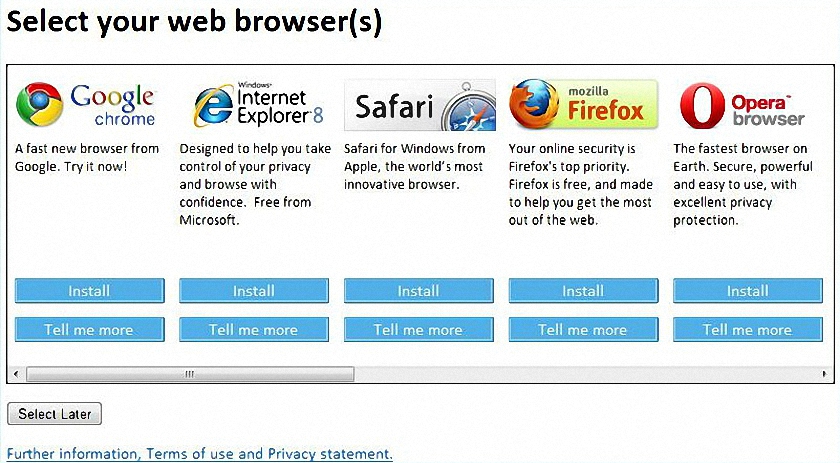
Browser Choice In Microsoft Windows Ends
Browser Choice – What’s That About In December 2009 the European Union obliged Microsoft to offer a choice of browsers to their European customers when they installed new versions of Windows. This browser choice was also delivered in updates to Windows and so the Browser Choice screen was born and has been with us ever since.…
-
Backdoor Trojan Regin Spying Since 2008
A recently discovered Backdoor Trojan Regin is a computer bug found by the software security company Symantec. Its purpose is to spy on the activities taking place on computers. It can collect passwords, capture screen images and even recover deleted files. The Backdoor Trojan Regin has been made to operate in five stages the last two being encrypted to…
-
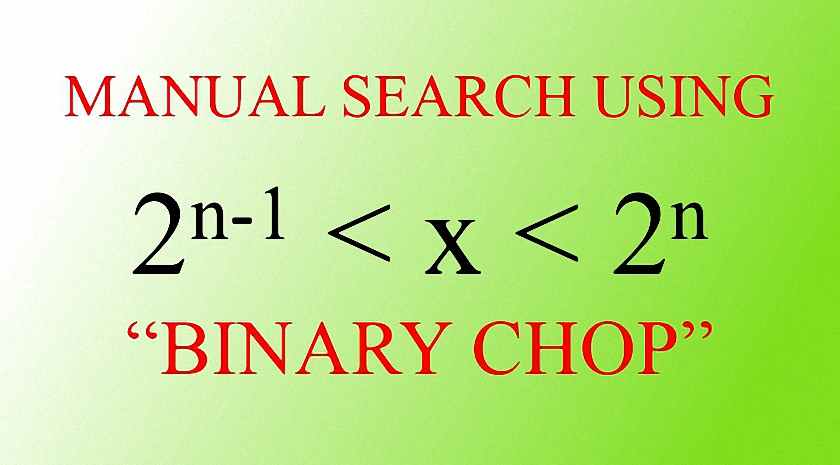
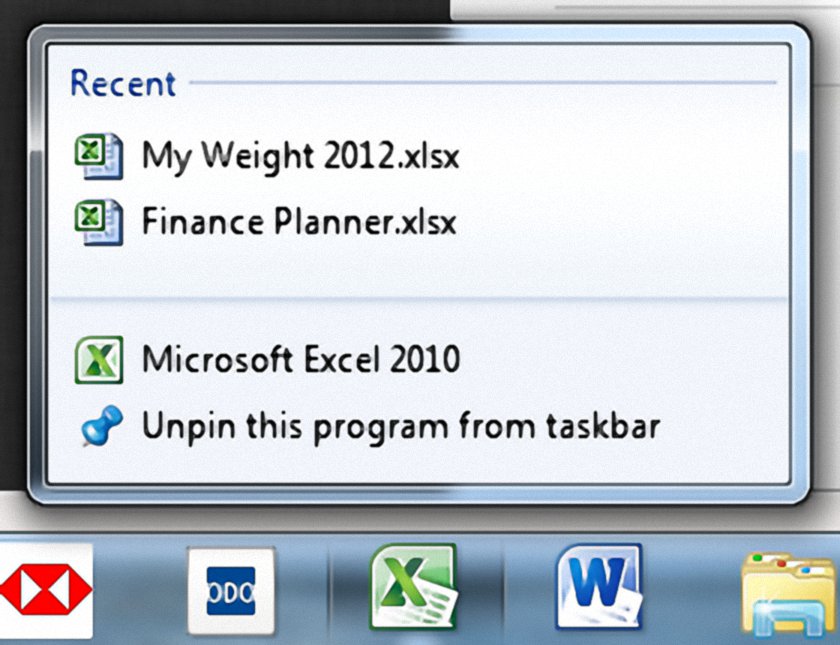
Manual Search Using Binary Chop
The Problem To Be Solved. A good friend of mine had found that an Excel spread sheet no longer had a formulae in a particular cell. It had a number there instead. This meant that any changes in other cells associated with the missing formulae had no effect on the result in the TOTAL column.…
-
Targeted Attacks via Internet Explorer Confirmed by Microsoft
There is a vulnerability (flaw) which allows targeted attacks via Internet Explorer versions 6 through 11 to be made on MS Windows PC’s. The attack seems complex to me and probably not easily made against the masses. The ultimate goal of an attacker would be to encourage a PC user to visit dangerous websites. Microsoft…
-

Bank Machines Will Use Windows XP Beyond The MS Deadline
Well, well, well, whose not keeping on top of things then. It looks like all the major banks. This article from ITPRO taken from Reuters points out that some major banks will not have updated their Automatic Telling Machines to Windows 7 by 8th April 2014. This is Microsoft’s published deadline after which there will…
-
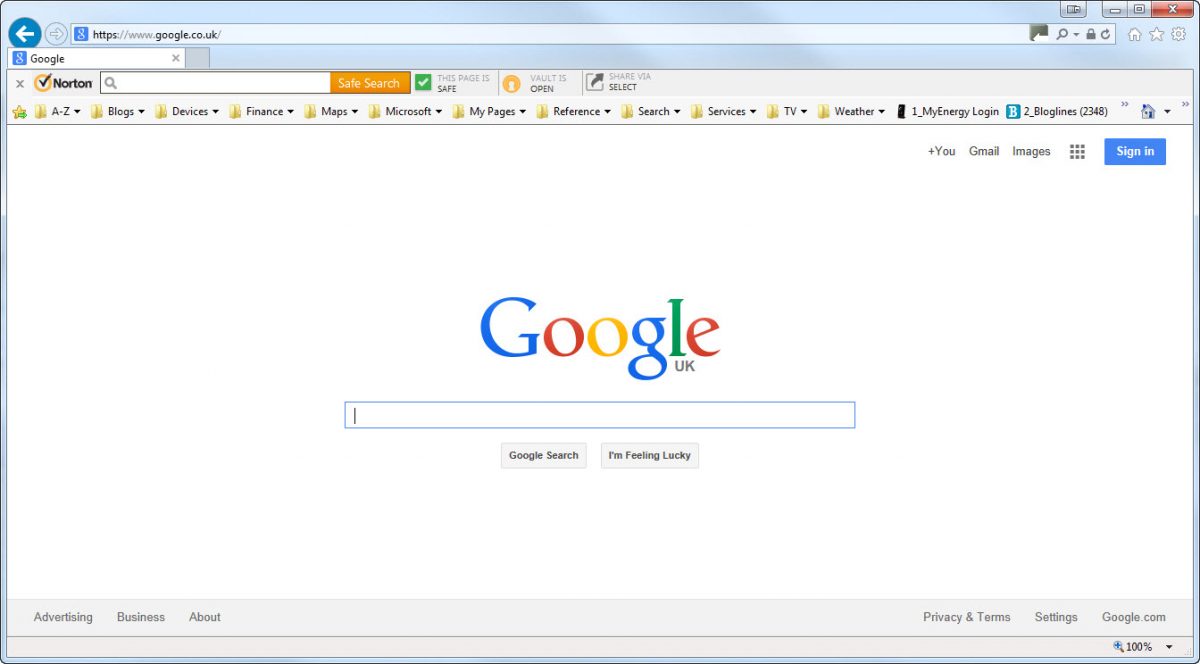
Make Google The Home Page In Windows 7
Introduction A friend found they had got MSN as their Home page and asked me how they could make Google the Home page in Windows 7. What They Saw I haven’t seen their screen but I would expect it to look like the screen shot above, when they select their Home page, with MSN showing. Here I…
-

Internet Explorer Suggested Sites – Not My Favourites
I don’t necessarily want Internet Explorer Suggested Sites on my Favourites Bar in Internet Explorer. I just want My Favourites. Yes, I’m talking about the Suggested Sites shortcut which appears on the Favourites Bar and defies all attempts to remove it permanently. Deleting the shortcut from the Favourites Bar does not prevent it from returning.
-
Employees Pose Security Risks To Businesses
Employees Pose Security Risks To Businesses Trend Micro says employees pose security risks to businesses by their carelessness. So don’t allow access to your business data through your employees. Data is exposed by Wi-Fi hijacking and by employees losing mobile devices. Read about it on IT PRO by clicking here.
-

Drag-n-Drop Context Menu in Windows
Drag-n-Drop Context Menu Discovered After Nearly Losing Files After many years I have just found that there is a specific Drag-n-Drop Context Menu, in Microsoft Windows 7 & Windows 10 at least. For years I avoided Drag-n-Drop in favour of Copy and Paste. This discovery came about after I found I was Moving files out of folders…
-
I Reduced Windows 7 Startup Time To Two Minutes
Introduction I have wanted a way to get a reduced windows 7 startup time for a while. I was concerned about the time it took from switch on to the point where all apps that start automatically were ready for use. This has generally increased over the years during the time I had previous versions…
-
IE9 Zero Day Vulnerability Fixed
For a week now it has been known that there is an IE9 Zero Day Vulnerability. Get This Zero Day Vulnerability Fixed Now Microsoft have published a fix which came to me today in the form of an update as follows (for Windows 7): Cumulative Security Update for Internet Explorer 9 for Windows 7 for x64-based Systems (KB2744842)…
-
Phishing Email NOT From TESCO Bank
Where Does This Email Pretend To Come From? This phishing email pretends to come from: Tesco Personal Finance customerservice@consumercardservicing.tescofinance.com. As you can see from the image of the email content below if you were to click on the link: http://www.tescobank.co.uk/1/2/TESCOCAM10;&user=% colin.ride@btinternet.com % . . . you will not go to a Tesco website. Look carefully…
-
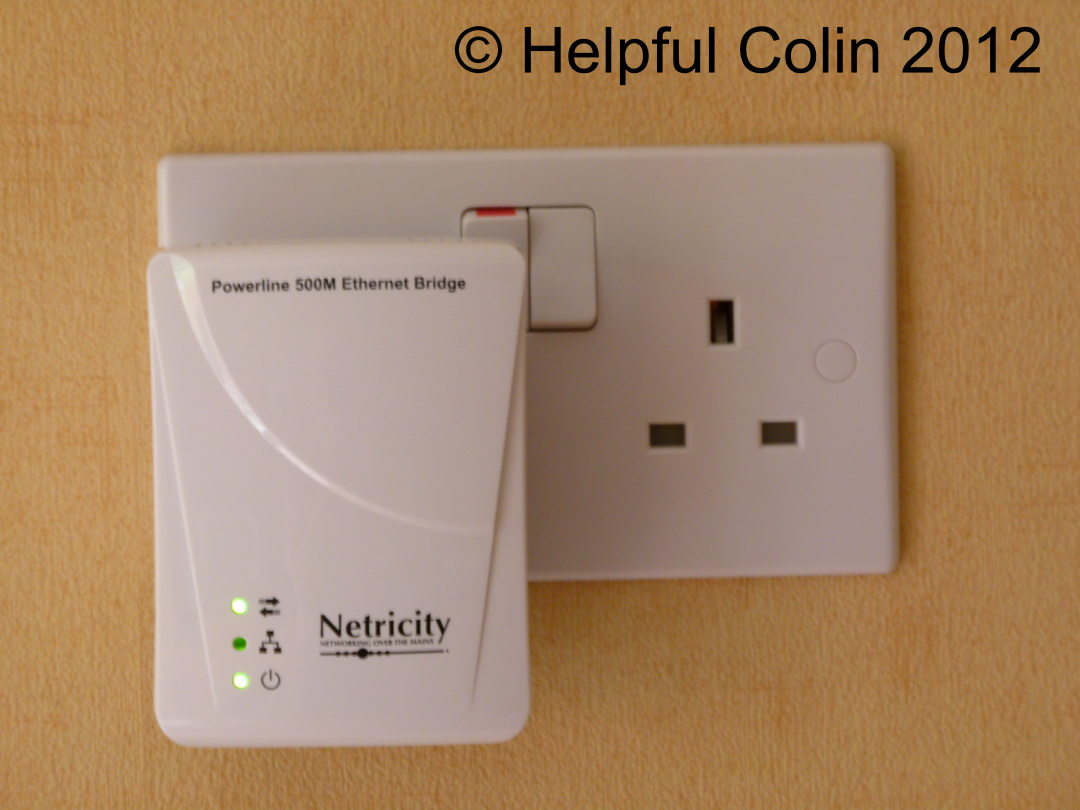
Netricity Ethernet Bridge Adapter Failed After 13 Months
Introduction Panic set in last night when I couldn’t access the Internet. Eventually I tried my laptop after checking the lights on my Home Hub and reset it a few times. That worked O.K. and in the end I deduced my power-line network had failed. It turned out that a Netricity Powerline 500M Ethernet Bridge Adapter…
-

One Mouse And Keyboard Can Control 1-4 Computers
Introduction Back in June 2012 I found this amazing software, Mouse without Borders from Microsoft Garage. It allows me to control 1-4 computers. Usually that is my desktop PC and my notebook with my desktop mouse and keyboard. I can move my pointer off the right-hand edge of my desktop screen and onto the left-hand…
-
PHISHING SPAM ALERT! Purporting to come from Amazon. BEWARE!
Further to my tweets this is the detail of spam I received today. I have unlinked the links (and coloured them orange) so you can’t get caught out: Your order has been successfully canceled. For your reference, here’s a summary of your order: You just canceled order #132-138566-4336469 placed on February 3, 2012. Status: CANCELED _____________________________________________________________________…
-
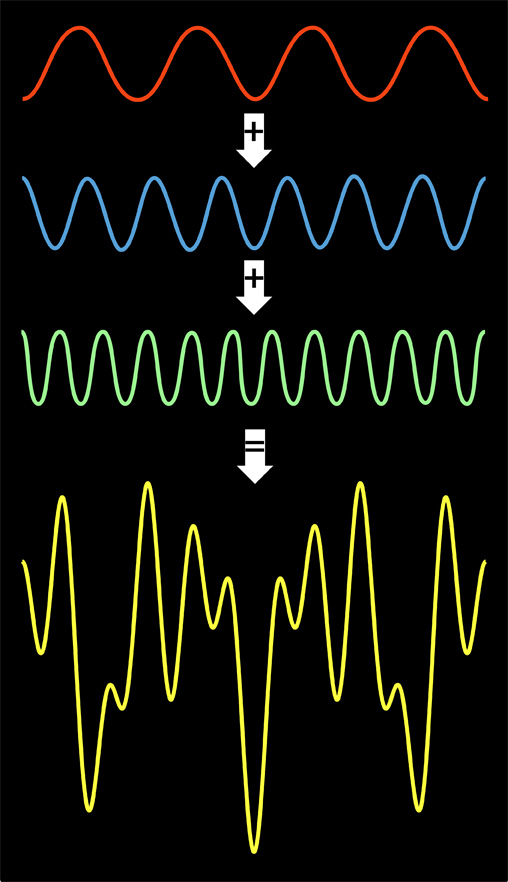
The Faster-Than-Fast Fourier Transform
Improving The Fast Fourier Transform To Make It Faster-Than-Fast The Faster-Than-Fast Fourier Transform can replace the Fast Fourier Transform to save processing time when digitising an analogue signal. For a large range of practically useful cases, MIT researchers find a way to increase the speed of one of the most important algorithms in the information…
-
iPad Survives Undamaged After Extreme Fall
Introduction It’s becoming quite popular to send cameras up to the edge of space for one reason or another. This is one of the latest which an iPad survives undamaged. See How An iPad Survives Undamaged After An Extreme Fall. NOTE: The article quotes, “….with the blackness of space and the bright curve of Earth providing a…
-
Using The Character Map Application In Windows
Accessing The Character Map Application It reminds me of an unusual dice when I see this icon. It has a beauty about it. What is it? It’s the icon representing the Character Map application in Windows 7, found on the Start Menu under Accessories > Ease of Access > System Tools. The Character Map application is stored…